If you have a Mac with an M1 chip, you can run iPhone and iPad apps and games right on your Mac. Apple has been steadily adding more capabilities to this feature, but the latest MacOS 11.3 update.
A new open source database, open source firmware on TP-Link routers, and more news; Upskill U Kicks Off Open Source Courses. As service providers seek to rapidly implement virtualization, open source software is emerging as a crucial tool in both expediting the software development process and creating an agile virtualized network architecture. Spotify Download Spotify. Mac OS X (Current 10.10 10.9 10.7-8)Windows (Current Vista)iOS; Android (Google Play Amazon)Spotify for other platforms.
Trade in with Apple
Turn an eligible device into credit towards a new one, or recycle it for free. Apple Trade In is good for you and the planet.
Get Support
Choose a product and we’ll find you the best solution.
Service and support from Apple experts
AppleCare products provide additional hardware service options and expert technical support from Apple.
Learn about AppleCare plansBeware of counterfeit parts
Some counterfeit and third party power adapters and batteries may not be designed properly and could result in safety issues. To ensure you receive a genuine Apple battery during a battery replacement, we recommend visiting an Apple Store or Apple Authorized Service Provider. If you need a replacement adapter to charge your Apple device, we recommend getting an Apple power adapter.
Also non-genuine replacement displays may have compromised visual quality and may fail to work correctly. Apple-certified screen repairs are performed by trusted experts who use genuine Apple parts.
Apple Service Programs
07/25 Update added below. This post was originally published on July 22nd, 2020.
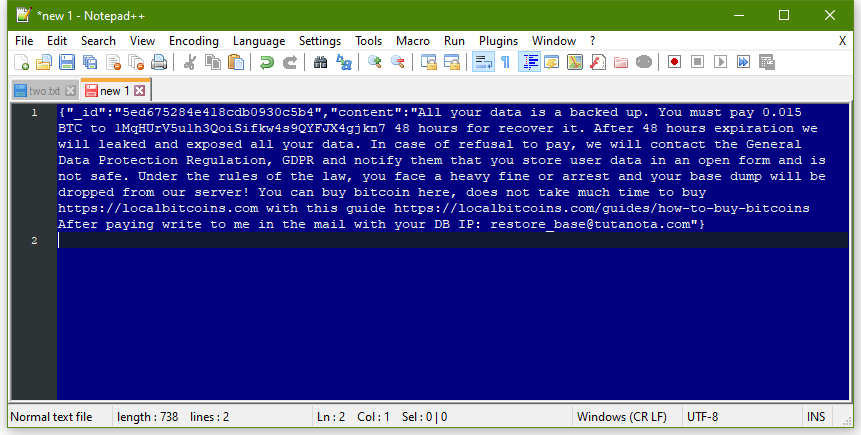
Hundreds of unsecured databases exposed on the public web are the target of an automated 'meow' attack that destroys data without any explanation.
The activity started recently by hitting Elasticsearch and MongoDB instances without leaving any explanation, or even a ransom note. Attacks then expanded to other database types and to file systems open on the web.
A quick search by BleepingComputer on the IoT search engine Shodan initially found dozens of databases that have been affected by this attack. Recently, the number of wiped databases increased to over 1,800.
These attacks have pushed researchers into a race to find the exposed databases and report them responsibly before they become 'meowed.'
Cat's out of the bag
One of the first publicly known examples of a Meow attack is an Elasticsearch database belonging to a VPN provider that claimed not to keep any logs.
Discovered by researcher Bob Diachenko, the database was initially secured in July only to become exposed again five days later.
The second time, though, the owner no longer received a well-intended notification. Instead, they got ‘meowed,’ with almost all records getting wiped.
Diachenko told BleepingComputer that there are not many details about the attacker or the purpose of their actions. He says that the attack appears to be an automated script that “overwrites or destroys the data completely.”
Researchers first observed the ‘meow’ database attacks at the beginning of the week. They could be the work of a vigilante trying to give administrators a hard lesson in security by raining destruction on unsecured data.
Victor Gevers, the chairman of the non-profit GDI Foundation, saw this type of attack, too. He says that the actor is also attacking exposed MongoDB databases, hitting as much as they can.
He also saw the first ‘meow’ attacks a few days ago, with a recent one occurring on July 22, just a couple of hours after a GDI volunteer disclosed it responsibly to the owner.
The researcher observed on Thursday that whoever is behind the 'meow' attack is apparently targeting any database that is insecure and reachable over the internet.
He saw these attacks.
07/25 Update: The Meow attacks continue to escalate with almost 4,000 databases deleted as of Saturday, July 25th.
A new search on Saturday using Shodan shows that more than 3,800 databases have entry names matching the 'meow' attack. More than 97% of them are Elastic and MongoDB.
While it is still not known why the threat actors are wiping databases, a security researcher named Anthr@X discovered that the attacks are being conducted via ProtonVPN IP addresses.
Obstructing researchers
If behind these incidents are positive intentions, sometimes nothing good comes out of them and valuable data that could be lost in the process.
Data leaks from unsecured MongoDB and Elasticsearch instances reachable over the public internet are on a descending curve, but there is still some “very sensitive” information exposed.
As Gevers puts it, “some leaks bring bad things to the light, which need to be shared,” and wiping them brings benefits to no one.
“It is becoming a race to find these leaks as early as possible. This reduces the amount of time that can be spent on researching and reporting” - Victor Gevers
Leaky Meow Mac Os 11
Whoever is behind the 'meow' attacks is likely to keep on targeting unsecured databases, aggressively destroying them. Administrators should make sure that they expose only what needs to be exposed and make sure the assets are properly secured.
Update [July 25, 2020]: Added image with overall status of 'meow' attacks from LeakIX. Recalculated amount of deleted databases due to Meow attacks.